The Human Firewall – and Modern Cyber Defense
Why Workplace Culture & The Human Factor Matter
properties.trackTitle
properties.trackSubtitle
In today's insurance market, organizations are expected to maintain rigorous security controls. Companies scrutinize the way the attack surface is protected by technical tools and processes. Yet, losses are still occurring.
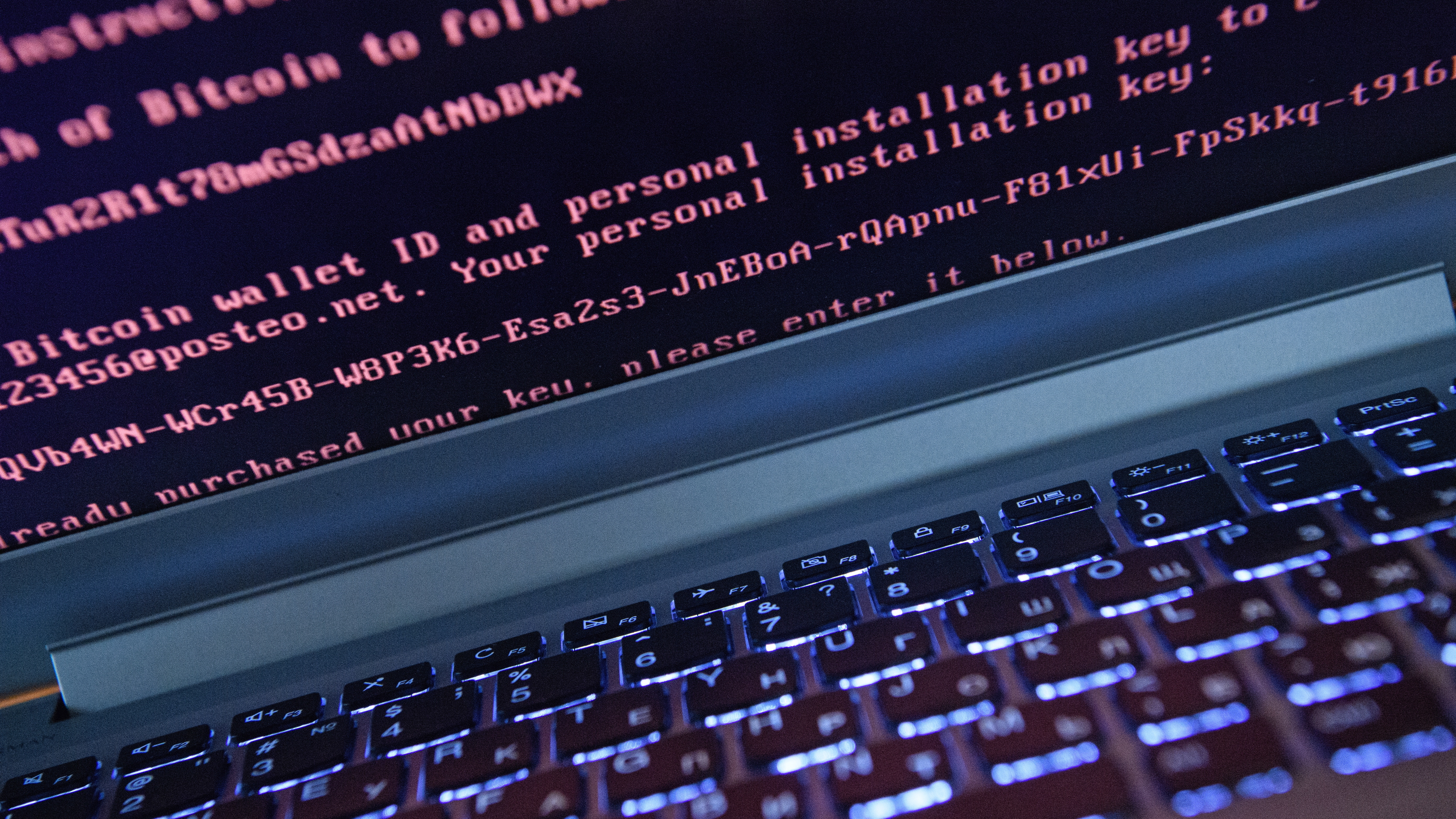
That's because something crucial is being left out of the picture. Presently, 90% of attacks are caused by human error [research from Stanford University from 2022]. 90% of ransomware attacks originated through a phishing email.
As persisting ransomware attacks fuel rising claims and increasing insurance rates, how can insureds and carriers work to flatten the curve? One key consideration is that organizations need to fortify the human firewall, and carriers must require it.
"We must expect organizations to harden their human defenses the same way we expect them to harden their systems," said Maria Long, Assistant Vice President, Cyber Underwriter & Risk Management Portfolio Leader for Munich Re Specialty.
Every single day workers are subject to phishing emails, CEO fraud attempts, spear phishing, and wire transfer fraud gimmicks. If the employee base can be trained, and their decision-making abilities tested, these attacks can be prevented at the human firewall.
Cyclical Effects of the Cyber Insurance Market and Risk Management Implementation
It's fair to say the cyber insurance market has played a significant role in hardening security controls, especially over the last year, as cyber entered a severe market correction.
By requiring best-in-class controls and business continuity measures, underwriters are courting organizations with favorable cybersecurity postures. The investments being made by insureds in order to maintain insurance cover serve both the insured and carrier – insulating both parties from frequency and severity losses.
So why are ransomware losses persisting? Because we are not appropriately spotlighting the critical need to train and educate our greatest security asset – humans.
"People must be acknowledged as a core security asset," said Long.
Insureds and carriers must view cyber posture through an additional lens; human defenses. This is accomplished through workplace culture, training, and phishing simulations. Even with increased cybersecurity budgets, something is amiss – less than 3% of those budgets are allocated to the human factor [research from Sanford University from 2022].
Training, Phishing and Culture
The solution is not revelational - it's tried, true, and logical. Training, phishing simulations, and workplace culture are the trifecta for building human defenses.
Training establishes baseline cyber hygiene knowledge and makes connections between information and application. Training should include live and computer-based modules. Phishing simulations allow employees to learn and even make mistakes in a controlled environment where they improve behavior and reflexes to these malicious emails.
When it comes to culture, stress and exhaustion lead to mistakes that can be costly. In environments where employees are burned out, they are more likely to fall victim to a phishing attack.
Organizations need to work on reducing burnout – thinking of it the same way productivity has been proven to go up when employees are given opportunities to decompress and achieve balanced workloads.
"When evaluating cyber risk, an organization lacking an awareness program is a prodrome to an eventual cyber-attack and should be considered a red flag," Long added.
She also stressed that underwriters need to evaluate training and awareness programs by asking the right questions. Method, frequency, and metrics are quality and success indicators.
Understanding whether a program is in place, for how long, how it is deployed, whether phishing simulations are provided as well as the frequency and click rates. Training and phishing simulations are a must-have combination – providing a sort of 1-2 punch by broadening knowledge and demonstrating good cyber behavior, improving employee reflexes.
What does a good training program look like?
It's important to recognize that not all training programs are built alike. When evaluating options and implementing training – what should organizations look for?
- Specific - Training content must align with organizational needs. Think about compliance, and train to the highest requirements for consistency across the footprint.
- Custom: Mixing computer-based learning and live learning can help address the needs of visual, auditory, and kinesthetic learners. Succinct, interactive videos are best.
- Dynamic: Training must be integrated with phishing simulations – those who fall for the phish will receive additional training.
- Measurable: The Learning Management System (LMS) should provide insights and metrics to establish progress over time and demonstrate value to stakeholders.
- Flexible: Options for SCORM compliant training modules – this means they can be imported into an organization's existing learning system.
- Relevant: Training content should be refreshed annually… at least.
- Reoccurring: Employees should receive training upon hire and then annually. Ad hoc prescriptive training should be provided to refresh and fortify knowledge.
Creating a strong cybersecurity culture
It's all about the "why" and the conversation should start from the top down. The key is to embed cyber hygiene into organizational culture, which is transformed from the top down – making the C-suite key stakeholders.
Leadership must understand the implications of phishing attacks and benefits of a strong cyber training and awareness program – integrating and aligning the "why" with the mission and values of the organization.
In other words, why should time and money be spent on this initiative? An organization cannot fulfill its mission to provide its services if its data is encrypted as a result of a phishing email. An organization cannot fulfill its value (and responsibility) to maintain confidentiality, integrity, and availability of its digital assets if they are encrypted and exfiltrated.
Buy-in is gained by communicating the implications and benefits, empowering the workforce as agents of protection and critical decisionmakers. The implications of phishing attacks include operational downtime, resulting in business interruption and revenue loss.
Reputational damage can occur, as stakeholders expect the organization to be responsible stewards of data – stakeholders lose faith in organizations that fall victim to cyber-attacks, especially when it's the stakeholder’s data at risk – viewing themselves as the victim and the organization as an irresponsible steward.
Employee data is at risk as well, particularly information maintained by human resources. Deploying a training and phishing program significantly reduces susceptibility to an attack, helping to maintain the organization's reputation and solvency by protecting personal, sensitive and proprietary information.
Those familiar with the psychological tactics of social engineering will likely recall that it typically includes a call to action, power and likability to persuade victims. This is because employees respond to these types of communications – we are wired to do so.
The very same psychological characteristics that cause us to fall victim to an attack can be engineered to create a strong cybersecurity culture. Organizations must treat employee cyber vigilance as a campaign – calling internal stakeholders to action, and empowering them with the tools & knowledge to protect their organization. This empowerment and collaboration toward a common goal translates to job satisfaction and embedded culture.
Through the lens of an underwriter
If our insureds already provide training and phishing simulations, we want to understand the phishing click rate in order to determine overall employee susceptibility. This is standard as we work to understand risk holistically; people – processes – technology. We want a 360-degree view of our insureds.
"We aren't just assessing your technical controls, because we recognize the implications of an insured that doesn’t invest in its cybersecurity culture," Long said.
Breaking the barriers to engagement - Munich Re Specialty has a vision
There are key barriers to engagement outside of cost. These include vendor exploration, contract negotiation, design, implementation, and stakeholder buy-in.
As we look to the future, we are evaluating solutions for our insureds with a vision to provide these tools as a part of the policy benefits. By breaking down barriers to implementation, we can help insureds to patch knowledge and behavior gaps, while shaping a more favorable risk profile.
We believe we can break down barriers for insureds by connecting insureds with best-in-class training products by vetting training tools, owning the contract, and providing customization and implementation white-gloving. By supporting our insureds in standing up and maintaining a strong program, we can save an organization time and money while simplifying the process.
Learn more about Munich Re Specialty at https://www.munichrespecialty.com/.
This article was produced by the R&I Brand Studio, a unit of the advertising department of Risk & Insurance, in collaboration with Munich Re Specialty. The editorial staff of Risk & Insurance had no role in its preparation
For additional insights and resources
Further information

About Munich Re Specialty
Munich Re Specialty – North America products and services are offered by and provided through insurance companies and producers/surplus lines brokers that are eligible or licensed in accordance with the laws and regulations of individual jurisdictions. Products and services are not available in every, and may vary by, jurisdiction. The information provided on this site is intended as general information only and does not constitute an offer to sell or a solicitation to purchase insurance or non-insurance products and services. Please be aware that the insurance policy and not any information provided on this site will form the contract between the parties thereto, and will govern in all cases. Munich Re Specialty – North America’s insurance products and services in the United States, Canada, and the United Kingdom are underwritten and provided by or through one or more of the insurers, producers/surplus lines brokers that are members of the Munich Re Group identified below. Each company is financially responsible only for insurance policies it has issued.
For more information on Munich Re Specialty, including licensing, regulatory-required, and other information on the operating companies, please click here.